Every organization manages access in some form. It might start with shared drives, role-based folders, or manual approval processes. Over time, those stop scaling. Teams grow. Systems multiply. Sensitive information spreads across tools. Without a structured way to control who can access what, risk and friction increase at the same time.
Access control software brings order to that complexity. It helps organizations define permissions clearly, enforce them consistently, and adapt them as roles change. When done well, access control supports security without slowing people down. Employees get access to what they need to do their jobs. Leaders gain visibility into how systems are used. IT teams reduce manual work and audit pressure.
The shift toward hybrid work has only amplified this need. Employees now access systems from different locations, devices, and networks. At the same time, organizations rely on more SaaS tools than ever. Each new tool introduces another layer of access to manage. Relying on disconnected systems or manual processes creates gaps that are difficult to track and harder to fix.
Modern access control software centralizes these decisions. It connects identity, permissions, and governance into a single framework. When access aligns with roles, policies, and workflows, security becomes part of how work happens, not a barrier to it. This is where platforms like Axero play a key role, connecting access control directly to how employees collaborate and share information every day.
Top 11 low-code platforms for internal applications for 2026
- Axero
- Okta
- Microsoft Entra ID (Azure Active Directory)
- Ping Identity
- SailPoint
- OneLogin
- CyberArk
- JumpCloud
- Duo Security
- IBM Security Verify
- RSA SecurID
What is access control software?
Access control software is used to manage and enforce who can view, edit, or manage systems, applications, and information within an organization. It defines permissions based on roles, groups, policies, or attributes, and ensures access aligns with business rules and security requirements.
At its core, access control answers three questions. Who is the user? What are they trying to access? Under what conditions should access be granted? Modern platforms handle this dynamically, adjusting permissions as employees join, change roles, or leave the organization.
Access control software often integrates with identity providers, directories, and business systems. This allows organizations to manage access centrally rather than configuring permissions tool by tool. It also supports auditing and reporting, which helps meet compliance requirements and internal governance standards.
In a digital workplace, access control is not limited to IT systems. It also applies to content, knowledge bases, collaboration spaces, and internal communications. When access control is embedded into everyday workflows, organizations reduce risk while keeping information accessible to the right people at the right time.
What to consider when choosing the right access control software
Choosing access control software requires balancing security, usability, and operational efficiency. The right platform should protect sensitive information while fitting naturally into how your organization works.
Centralized identity and role management
A strong solution allows you to manage users, roles, and groups from one place. Centralization reduces errors and ensures access rules stay consistent across systems and content.
Integration with your existing tools
Access control should integrate with your intranet, collaboration platforms, HR systems, and cloud applications. This reduces duplication and keeps access aligned with real organizational structures.
Granular permission controls
Look for flexible permission models. You should be able to define access at different levels, from systems and applications down to individual documents or pages.
Automation and lifecycle management
Automated provisioning and deprovisioning reduce manual work and risk. Access should update automatically when roles change or employees leave.
Visibility, auditing, and governance
Clear reporting and audit trails help you understand who has access to what. This supports compliance, internal reviews, and ongoing governance.
11 best access control software
1. Axero
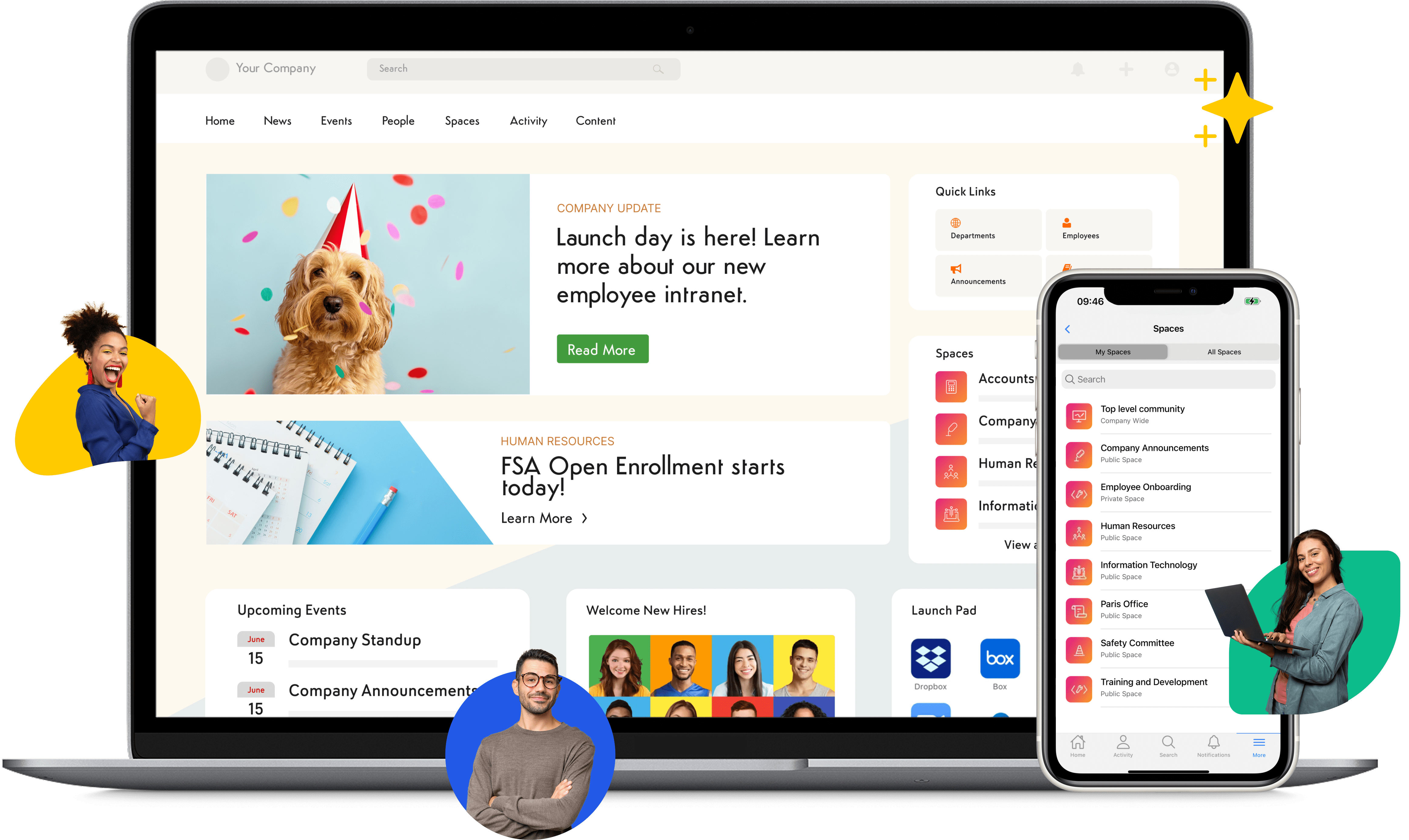
Axero approaches access control through the lens of the digital workplace. Rather than treating permissions as a standalone security layer, Axero embeds access control directly into how employees collaborate, share knowledge, and communicate. This makes access management practical, visible, and easier to govern across teams.
Axero allows administrators to define access at multiple levels, including sites, pages, documents, workspaces, and features. Permissions align with roles, departments, and groups, which keeps access consistent as the organization changes. When combined with Axero’s intranet structure, access control becomes part of everyday workflows rather than an IT-only task.
For organizations focused on internal communication and knowledge sharing, this approach reduces friction. Employees see relevant content without being overwhelmed. Sensitive information stays protected without relying on complex external tools. Administrators maintain oversight without constant manual updates.
Axero also integrates with identity providers and directory services, which supports centralized user management. This ensures access reflects real employee status and organizational structure at all times.
Key features of Axero
- Role-based access control: Align permissions with departments, teams, and job functions to keep access accurate as roles evolve.
- Content-level permissions: Control access to pages, files, and workspaces to protect sensitive information without restricting collaboration.
- Directory and identity integrations: Sync users and groups to reduce manual provisioning and maintain governance.
Best for: Organizations that want access control embedded into their intranet, knowledge management, and internal communication strategy.
2. Okta
Okta is widely known for its identity and access management capabilities, particularly in SaaS-heavy environments. It focuses on centralized authentication and authorization, allowing organizations to manage access across a large ecosystem of applications from a single platform.
Okta supports single sign-on, multi-factor authentication, and lifecycle management. This helps reduce password fatigue while strengthening security. Access policies can be defined based on roles, devices, and contextual factors, which supports more adaptive access decisions.
For IT teams, Okta simplifies onboarding and offboarding by automating access changes across connected applications. This reduces the risk of lingering access and improves compliance. Its large integration network makes it suitable for organizations using many third-party tools.
However, Okta focuses primarily on application access rather than content-level governance. Organizations often pair it with other platforms to manage internal collaboration and knowledge access more effectively.
Key features of Okta
- Single sign-on: Centralize authentication across cloud applications to improve user experience and security.
- Adaptive access policies: Apply conditional rules based on user context and risk signals.
- Lifecycle automation: Automate provisioning and deprovisioning across connected systems.
Best for: Organizations managing access across many SaaS applications that need centralized identity control.
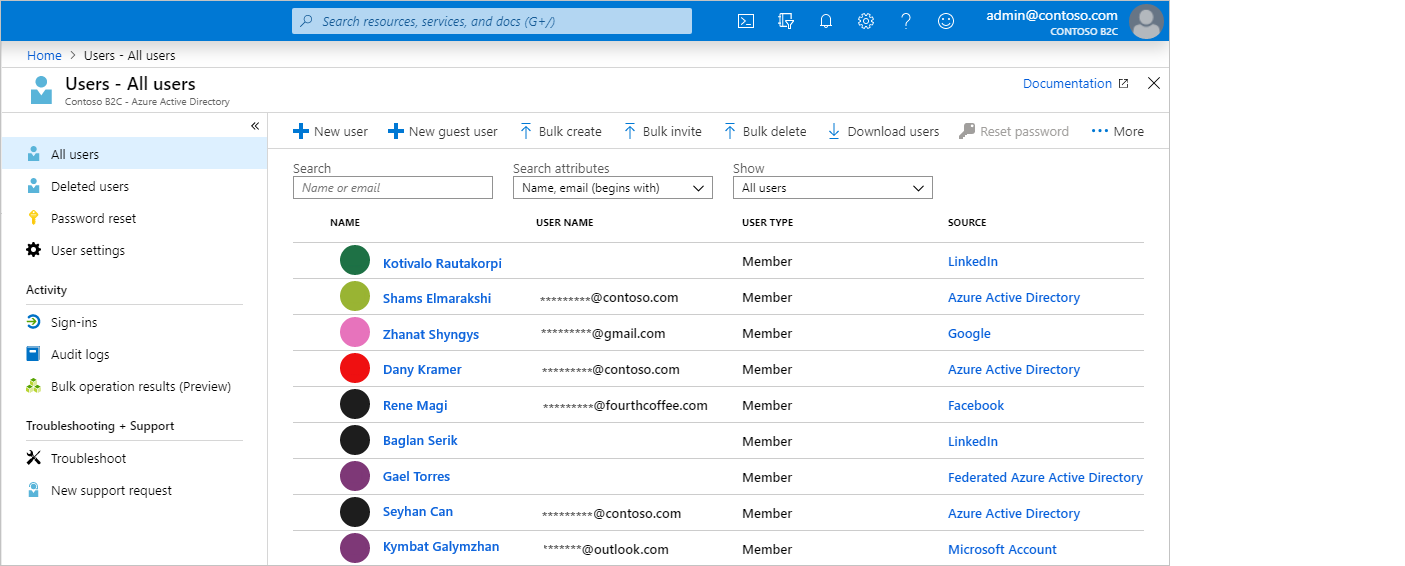
3. Microsoft Entra ID (Azure Active Directory)
Microsoft Entra ID provides identity and access management for organizations operating within the Microsoft ecosystem. It connects users, devices, and applications under a unified directory, which simplifies access control across Microsoft and third-party tools.
The platform supports role-based access, conditional access policies, and strong authentication methods. These capabilities allow organizations to define access rules that adapt to user behavior, location, and device compliance.
Entra ID integrates tightly with Microsoft 365, Azure services, and Windows environments. This makes it a natural choice for organizations already invested in Microsoft’s stack. IT teams benefit from centralized management and built-in reporting tools that support audits and compliance.
Like other identity-first platforms, Entra ID focuses on authentication and application access. Content-level access control often relies on configuration within connected tools rather than a unified intranet layer.
Key features of Microsoft Entra ID
- Conditional access policies: Enforce access rules based on risk, device status, and user context.
- Role-based access control: Assign permissions across Microsoft services and integrated applications.
- Deep Microsoft integrations: Manage access consistently across Microsoft 365 and Azure environments.
Best for: Organizations deeply invested in Microsoft tools that need centralized identity and access management.
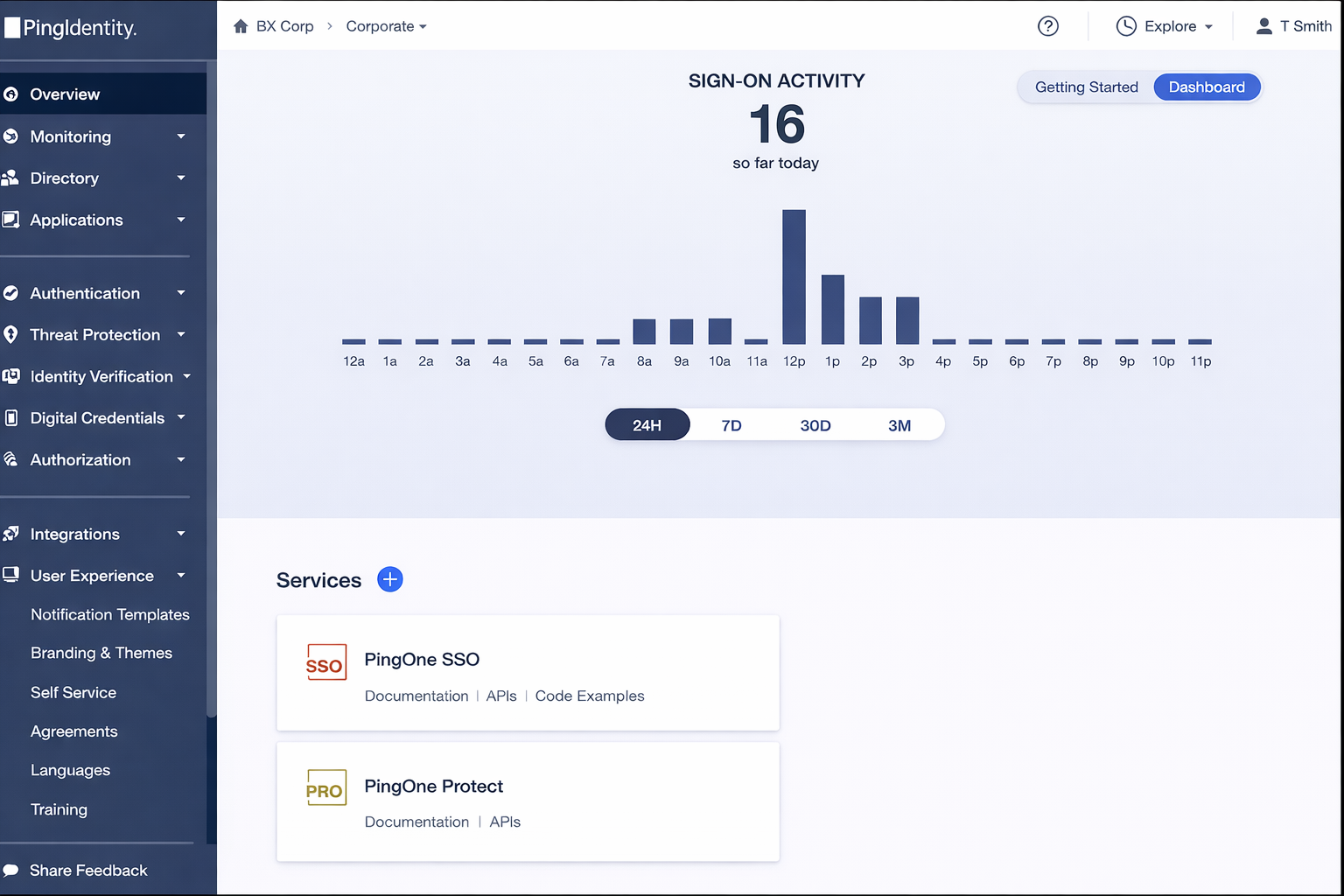
4. Ping Identity
Ping Identity focuses on enterprise-grade identity security with strong access control and authentication capabilities. It is designed for organizations that need flexible policies across complex environments, including hybrid and cloud infrastructures.
Ping Identity allows administrators to define access rules based on user identity, device posture, and contextual signals. This supports adaptive access decisions without forcing users through unnecessary friction. Its single sign-on and multi-factor authentication features help organizations reduce credential risk while maintaining a smooth login experience.
The platform is often used in environments where regulatory requirements are strict and integrations are extensive. Ping Identity connects with a wide range of applications and identity sources, which makes it suitable for larger enterprises with layered systems.
As with many identity-centric platforms, Ping Identity focuses primarily on authentication and authorization rather than day-to-day content governance. Organizations often rely on complementary tools to manage access to internal knowledge and collaboration spaces.
Key features of Ping Identity
- Adaptive authenticationt: Apply access rules based on risk signals, devices, and user behavior.
- Enterprise SSO: Centralize access across cloud and on-premises applications.
- Policy-driven access control: Define flexible rules that align with security and compliance needs.
Best for: Large organizations with complex identity requirements and strict security policies.
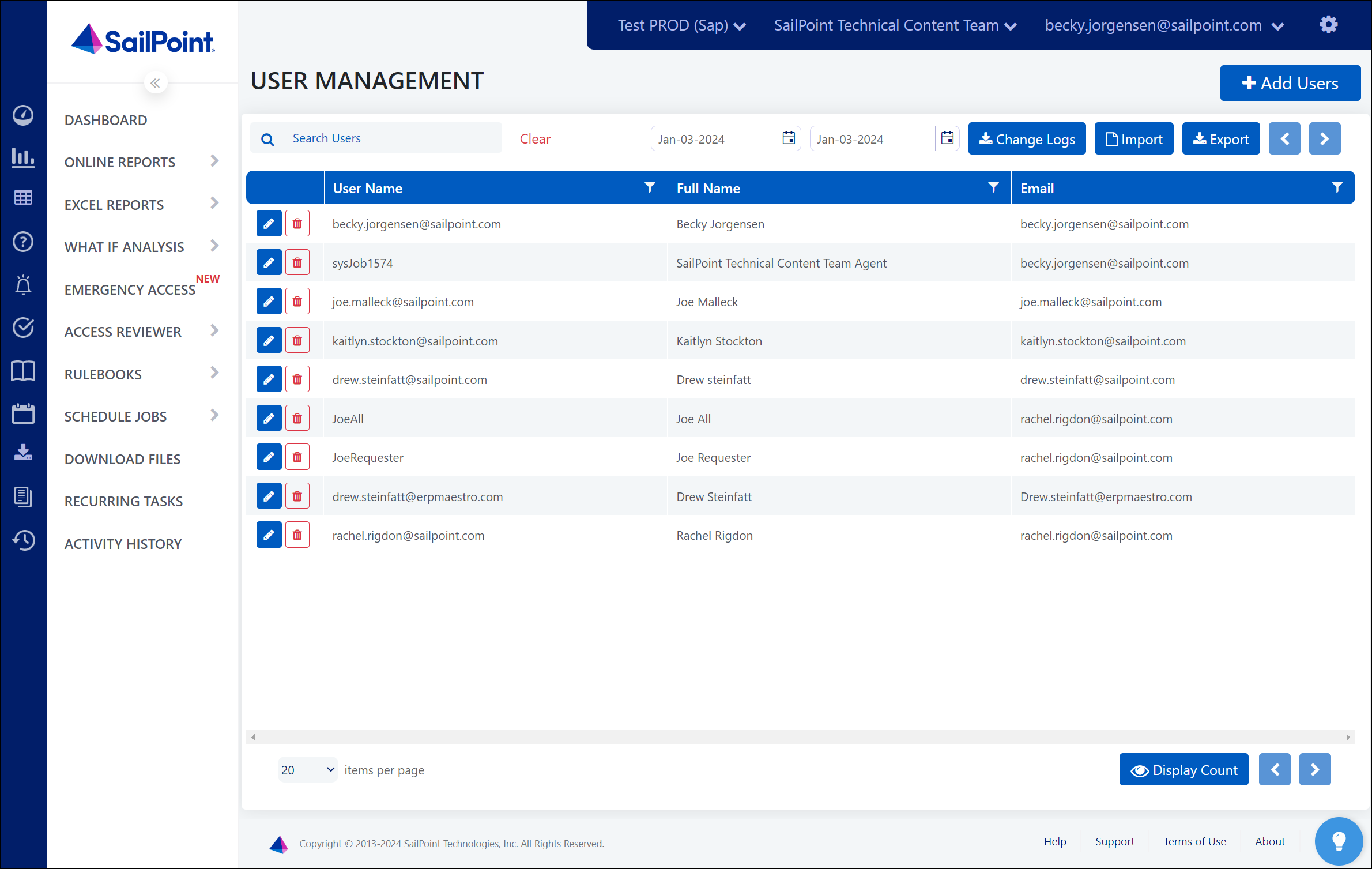
5. SailPoint
SailPoint specializes in identity governance and administration. Its strength lies in managing access at scale, with a focus on compliance, risk reduction, and visibility into user entitlements across systems.
SailPoint provides tools for role modeling, access reviews, and certification campaigns. These features help organizations understand who has access to what and why. Automated workflows support access requests, approvals, and revocations, which reduces manual effort and audit findings.
The platform is commonly used in regulated industries where access governance must be documented and reviewed regularly. SailPoint’s reporting and analytics help organizations demonstrate compliance and identify excessive or inappropriate access.
While powerful, SailPoint can require careful planning and administration. It is often paired with user-facing platforms, such as intranets, to ensure access decisions translate cleanly into everyday employee experiences.
Key features of SailPoint
- Access governance: Conduct reviews and certifications to maintain compliant access models.
- Role management: Define and refine roles to reduce overprovisioning.
- Automated workflows: Streamline access requests and approvals.
Best for: Organizations with strong compliance requirements and complex access governance needs.
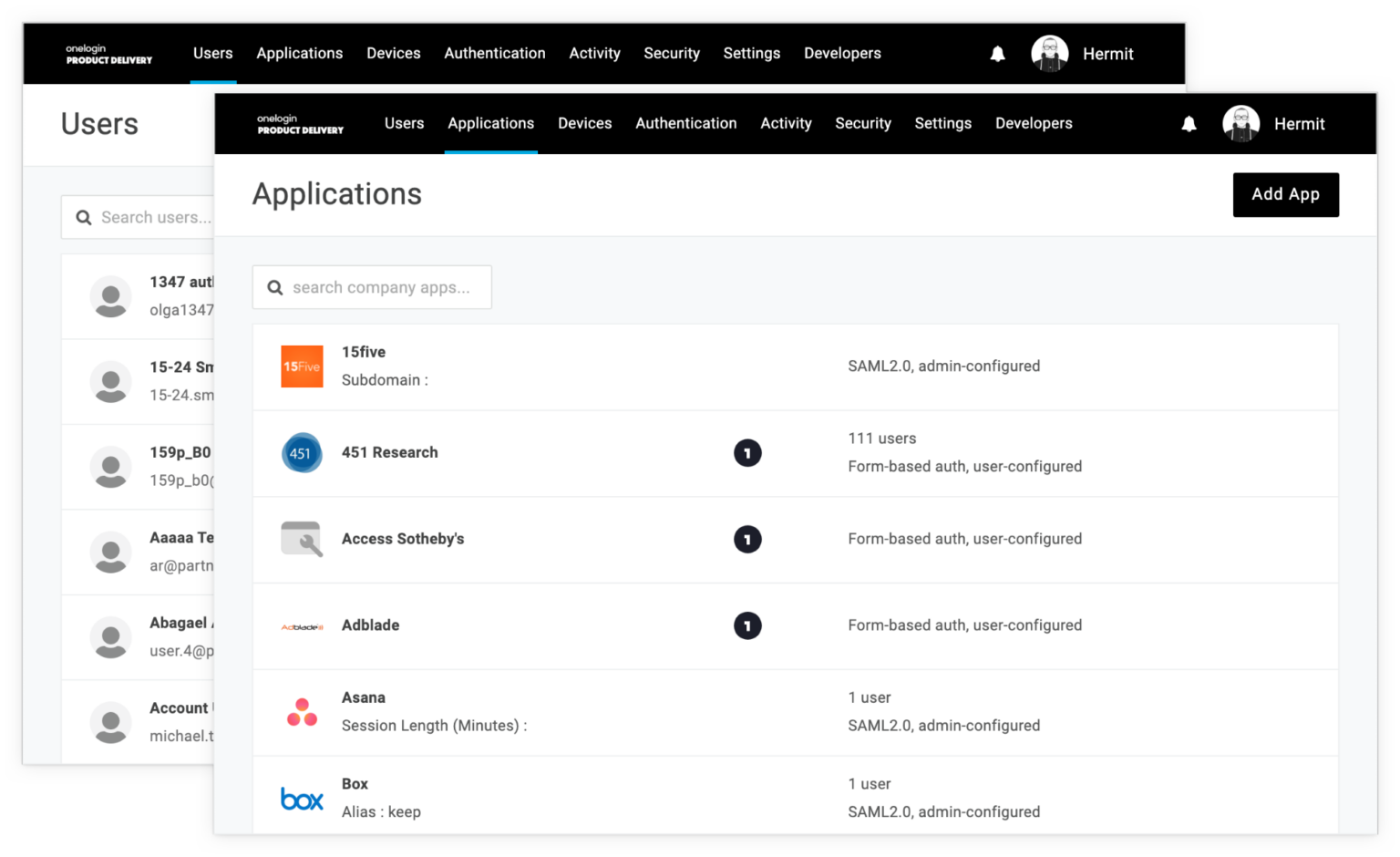
6. OneLogin
OneLogin offers cloud-based identity and access management designed to simplify authentication and user lifecycle management. It focuses on reducing login friction while maintaining consistent access control across applications.
The platform provides single sign-on, multi-factor authentication, and directory integrations. These features help centralize access management and reduce reliance on passwords. OneLogin’s user provisioning capabilities ensure access updates automatically when roles change.
OneLogin is often used by mid-sized organizations looking for a balance between security and usability. Its interface is approachable, and setup tends to be faster than more complex enterprise platforms.
As with other IAM tools, OneLogin primarily manages application access. Organizations still need complementary systems to govern access to internal content, collaboration spaces, and knowledge repositories.
Key features of OneLogin
- Cloud-based SSO: Simplify access to applications with a single login experience.
- User provisioning: Automatically manage access throughout the employee lifecycle.
- Multi-factor authentication: Add an extra layer of security without heavy complexity.
Best for: Mid-sized organizations seeking straightforward identity and access management.
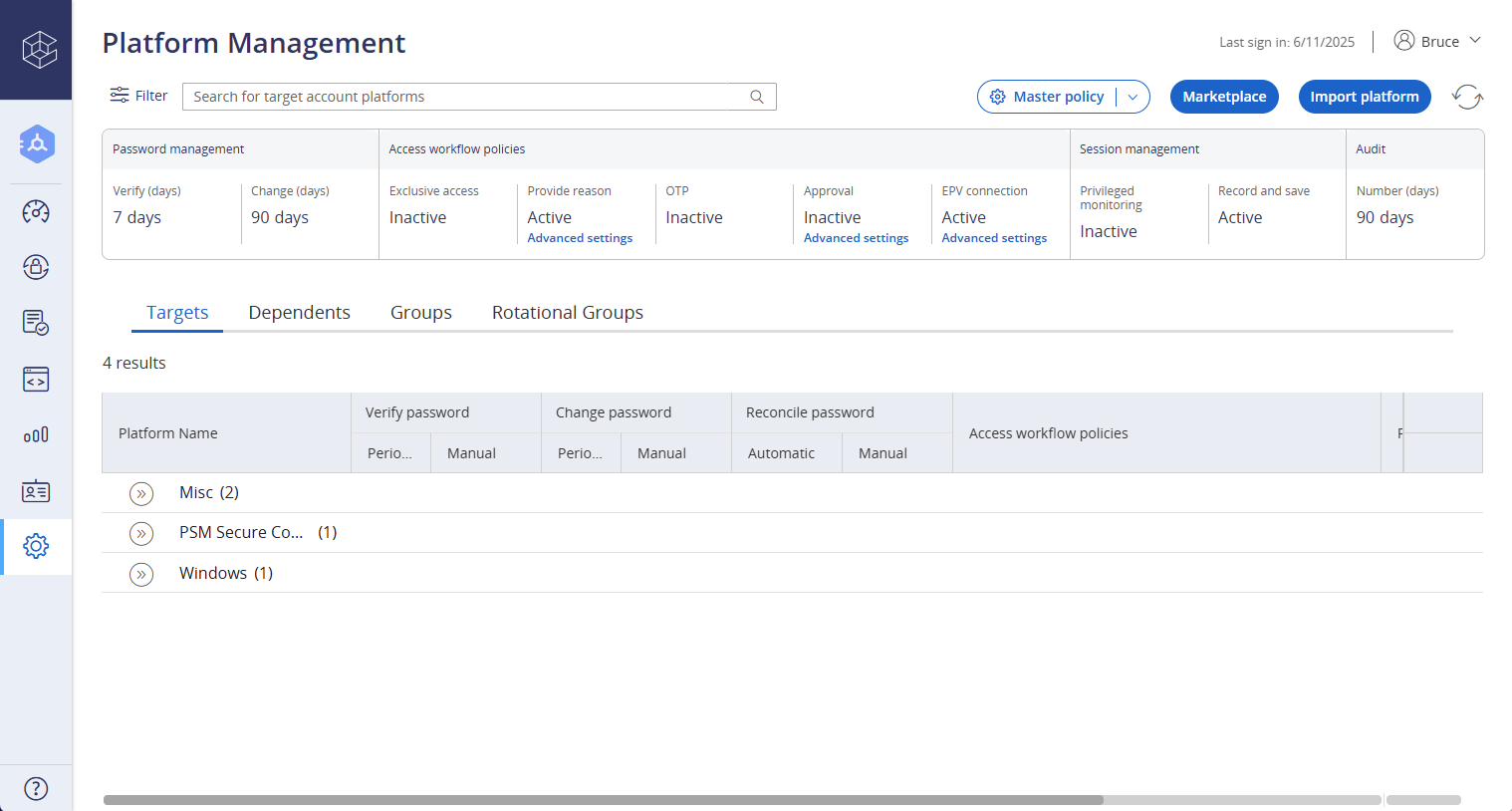
7. CyberArk
CyberArk is best known for privileged access management, with a strong focus on protecting high-risk accounts, credentials, and systems. Its access control capabilities are designed to reduce exposure around administrator accounts and sensitive infrastructure.
The platform enforces strict controls around privileged credentials, including vaulting, session monitoring, and just-in-time access. This limits standing access and reduces the attack surface. CyberArk also provides detailed audit trails, which supports investigations and compliance reviews.
CyberArk is commonly used in environments where security risk is high and access must be tightly governed. It works well alongside broader identity platforms, handling privileged access while other tools manage standard user access.
Because of its specialized focus, CyberArk is not typically used for general employee content or collaboration access. Organizations often integrate it into a wider access control ecosystem.
Key features of CyberArk
- Privileged access management: Protect and control administrator and high-risk accounts.
- Credential vaulting: Secure sensitive credentials and reduce exposure.
- Session monitoring: Record and audit privileged sessions for governance.
Best for: Organizations that need strong control over privileged and administrative access.
8. JumpCloud
JumpCloud combines directory services with identity and device management. It is designed to centralize access control across users, devices, and applications.
The platform allows administrators to manage user identities, enforce device policies, and control application access from one interface. This is particularly useful for organizations with distributed or remote teams using multiple device types.
JumpCloud supports single sign-on and directory integrations, which simplifies access management without relying on traditional on-premises directories. Its device-level controls add an extra layer of governance.
JumpCloud works well for organizations looking to consolidate identity and device management. Content and knowledge access typically requires additional platforms to complete the digital workplace picture.
Key features of JumpCloud
- Cloud directory services: Manage users without on-premises infrastructure.
- Device management: Enforce access policies across user devices.
- Application access control: Centralize authentication and authorization.
Best for: Organizations with remote teams that need unified user and device access control.
9. Duo Security
Duo Security focuses on strengthening access control through multi-factor authentication and secure access policies. It is widely used to add an extra layer of protection to applications, systems, and remote access scenarios.
Duo integrates with a broad range of applications, VPNs, and identity providers. This allows organizations to enforce consistent authentication policies without replacing their existing access infrastructure. Its device health checks add context to access decisions, helping reduce risk from unmanaged endpoints.
The platform is often adopted to improve security quickly, especially for remote or hybrid teams. Duo’s user experience is simple, which supports adoption without heavy training.
Duo primarily enhances authentication rather than managing granular access to internal content. Organizations typically pair it with identity or intranet platforms to cover broader access governance needs.
Key features of Duo Security
- Multi-factor authentication: Strengthen login security across applications and systems.
- Device trust checks: Add context to access decisions based on device posture.
- Wide integrations: Extend protection without disrupting existing workflows.
Best for: Organizations prioritizing stronger authentication for users and remote access.
10. IBM Security Verify
IBM Security Verify delivers identity and access management with a strong emphasis on enterprise governance and risk management. It supports centralized access control across applications and systems, backed by IBM’s security expertise.
The platform provides single sign-on, adaptive access policies, and lifecycle management. Its analytics and reporting tools help organizations understand access patterns and detect anomalies. This supports informed security decisions and compliance efforts.
IBM Security Verify is commonly used in large organizations with complex IT environments. It integrates with existing directories and enterprise systems, which helps maintain consistency across access policies.
As with many enterprise IAM solutions, content-level access and employee-facing governance often rely on additional platforms to complete the digital workplace experience.
Key features of IBM Security Verify
- Adaptive access policies: Adjust access based on risk and context.
- Enterprise reporting: Gain visibility into access patterns and anomalies.
- Lifecycle management: Automate access changes across systems.
Best for:Large enterprises needing scalable and governed access control.
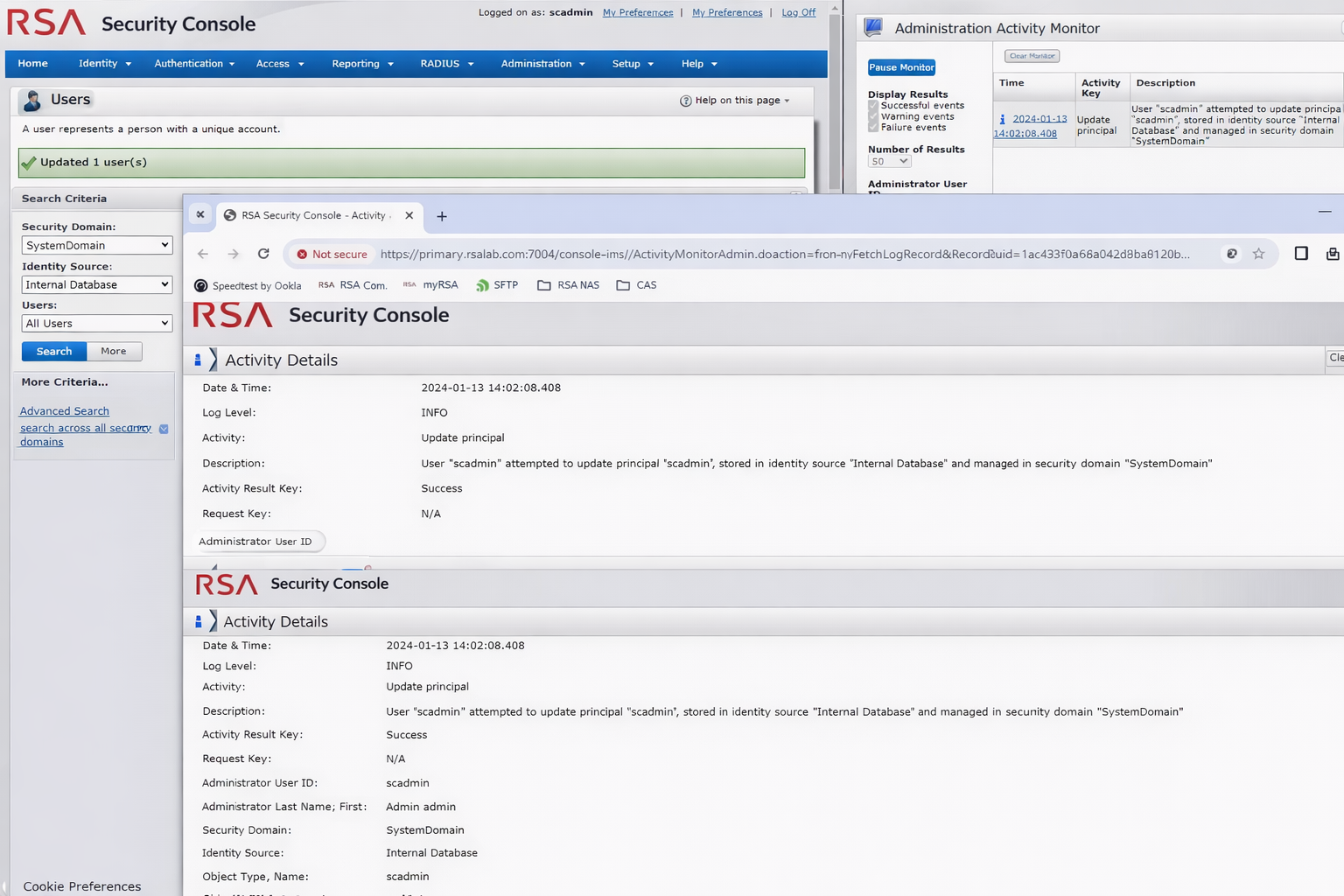
11. RSA SecurID
RSA SecurID is known for its strong authentication and access security capabilities. It focuses on protecting access to critical systems through multi-factor authentication and risk-based controls.
The platform supports hardware and software authentication methods, which provides flexibility across different security requirements. Risk-based policies help reduce friction for low-risk access while increasing scrutiny when needed.
RSA SecurID is often used in regulated environments where authentication standards are strict. It integrates with existing identity systems to enhance access control without a full platform replacement.
Like other authentication-focused tools, RSA SecurID complements broader access and content governance platforms rather than replacing them.
Key features of RSA SecurID
- Strong authentication: Support multiple MFA methods for secure access.
- Risk-based access: Adjust controls based on user behavior and context.
- Enterprise integrations: Enhance security across existing systems.
Best for: Organizations requiring high-assurance authentication for sensitive systems.
Choosing the right access control software for your organization
Access control touches every part of your organization, from IT security to daily collaboration. The right solution should protect sensitive information while supporting how your people actually work.
Identity-first platforms excel at authentication and application access. Governance-focused tools provide visibility and compliance. But access does not stop at systems and logins. Employees also need controlled access to knowledge, communication, and shared workspaces.
This is where Axero stands apart. By embedding access control directly into the intranet and digital workplace, we help organizations govern information where work happens. Permissions stay aligned with roles, content stays relevant, and employees stay productive.
If you are looking to simplify access control while strengthening internal communication and knowledge sharing, book a demo and see how Axero can support your access strategy.
























 info@axerosolutions.com
info@axerosolutions.com 1-855-AXERO-55
1-855-AXERO-55



