Modern organizations manage access across dozens of systems, tools, and departments. As teams grow and work becomes more distributed, controlling who can see, edit, approve, or manage information becomes harder to maintain through manual processes alone.
User permissions management software provides structure, consistency, and accountability. It helps organizations define roles, assign access logically, and reduce risk without slowing people down. When permissions are clear and enforced centrally, employees spend less time waiting for access and IT teams regain control over security and compliance.
This category of software also plays a major role in employee experience. When access aligns with job responsibilities, people can do their work without friction. New hires onboard faster. Role changes feel seamless. Offboarding happens cleanly and securely.
Not all tools approach permissions in the same way. Some focus heavily on identity governance. Others lean toward access control across applications. The most effective platforms balance security, usability, and integration with the rest of your digital workplace.
Below, we break down what user permissions management software is, what to consider when choosing a solution, and how the leading platforms compare, starting with Axero.
Top 11 user permissions management software for 2026
- Axero
- Okta
- Microsoft Entra ID
- JumpCloud
- OneLogin
- SailPoint
- Ping Identity
- CyberArk
- ManageEngine Identity Manager Plus
- Auth0
- IBM Security Verify
What is user permissions management software?
User permissions management software helps organizations control who can access specific systems, content, and actions across their digital environment. It defines what users are allowed to see and do based on roles, teams, locations, or responsibilities.
At its core, this software replaces ad hoc access decisions with structured rules. Instead of granting permissions one by one, administrators can assign access through predefined roles or groups. This ensures consistency and reduces the risk of overexposure to sensitive information.
Permissions management also supports compliance and security policies. It creates clear audit trails, enforces least-privilege access, and simplifies reviews when roles change or employees leave.
In modern workplaces, permissions management extends beyond IT systems. It applies to intranets, knowledge bases, workflows, and collaboration spaces. When integrated into a central platform, permissions become easier to manage and easier for employees to understand.
What to consider when choosing the right user permissions management software
Choosing the right solution starts with understanding how access is used across your organization. Permissions should support how people actually work, not force rigid structures that slow teams down.
Role-based access control
Look for software that allows you to define roles based on job function, department, or responsibility. This makes access easier to manage at scale and reduces manual updates.
Ease of administration
Permissions should be simple to assign, review, and adjust. Clear interfaces and logical hierarchies reduce errors and save IT time.
Integration with existing tools
Your permissions system should connect with the platforms you already use, including identity providers, collaboration tools, and intranet software.
Audit and compliance support
Strong reporting and visibility help you track access changes, run reviews, and meet internal or external compliance requirements.
Employee experience
Permissions should feel invisible to employees. When access is accurate from day one, people stay productive and engaged.
11 best user permissions management software
1. Axero
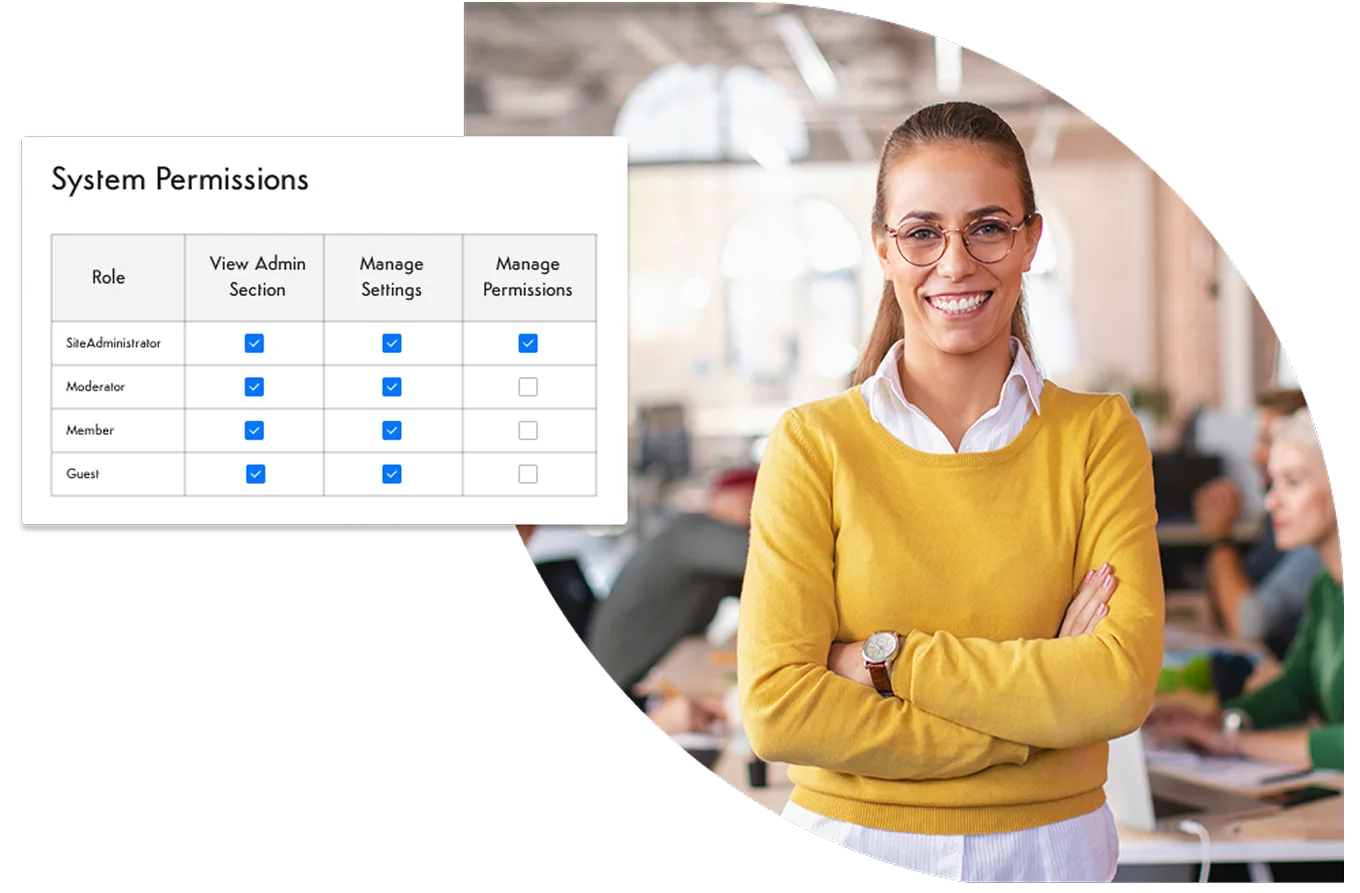
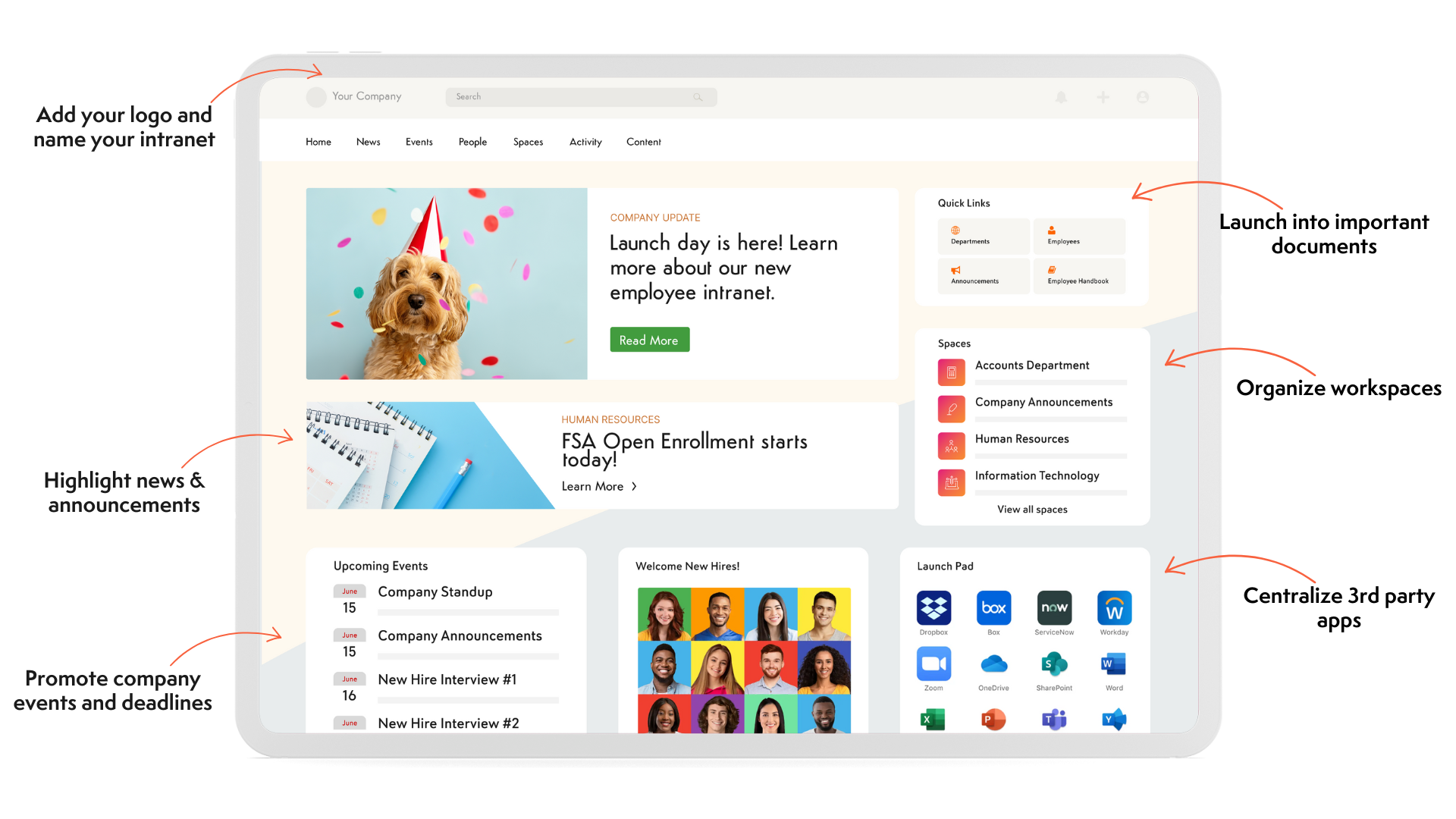
Axero approaches user permissions management as part of a broader digital workplace strategy. Rather than treating access control as a standalone security function, Axero embeds permissions directly into how employees interact with content, tools, and workflows.
Permissions in Axero are role-based and highly configurable. You can control access at the site, page, app, and content level, ensuring employees see only what is relevant to their role. This reduces noise while protecting sensitive information. Administrators can manage permissions centrally without complex rule building or scripting.
What sets Axero apart is how permissions support collaboration and engagement. Teams can securely share knowledge, manage workflows, and communicate without risking oversharing. Permissions also adapt easily as roles change, which simplifies onboarding, internal mobility, and offboarding.
Because Axero combines permissions with intranet, knowledge management, and workflow capabilities, organizations avoid managing access across disconnected systems. Everything lives in one platform that employees actually use.
Key features of Axero
- Granular content permissions: Control access at every level to keep information relevant and secure.
- Role-based access management: Assign permissions by role or group to simplify administration.
- Integrated digital workplace: Manage access across intranet pages, tools, and workflows in one place.
Best for: Organizations that want permissions management embedded into a central employee platform.
2. Okta
Okta is widely known for identity and access management, with a strong focus on secure authentication and application access. Its permissions management capabilities center around controlling user access to cloud-based tools through centralized identity policies.
Administrators can define access rules based on user attributes, group membership, or device context. This makes Okta effective for organizations managing many third-party applications. Access can be provisioned and deprovisioned automatically, which reduces manual effort and security gaps.
Okta works well in complex IT environments but often operates separately from employee-facing platforms. Permissions are strong at the application level, though less focused on content-level access or internal collaboration spaces.
For organizations prioritizing application security and single sign-on, Okta remains a reliable option.
Key features of Okta
- Centralized identity management: Control access to cloud applications from one directory.
- Automated provisioning: Assign and remove access as users join or leave.
- Policy-based access rules: Enforce security conditions across devices and locations.
Best for: IT teams managing access across many cloud applications.
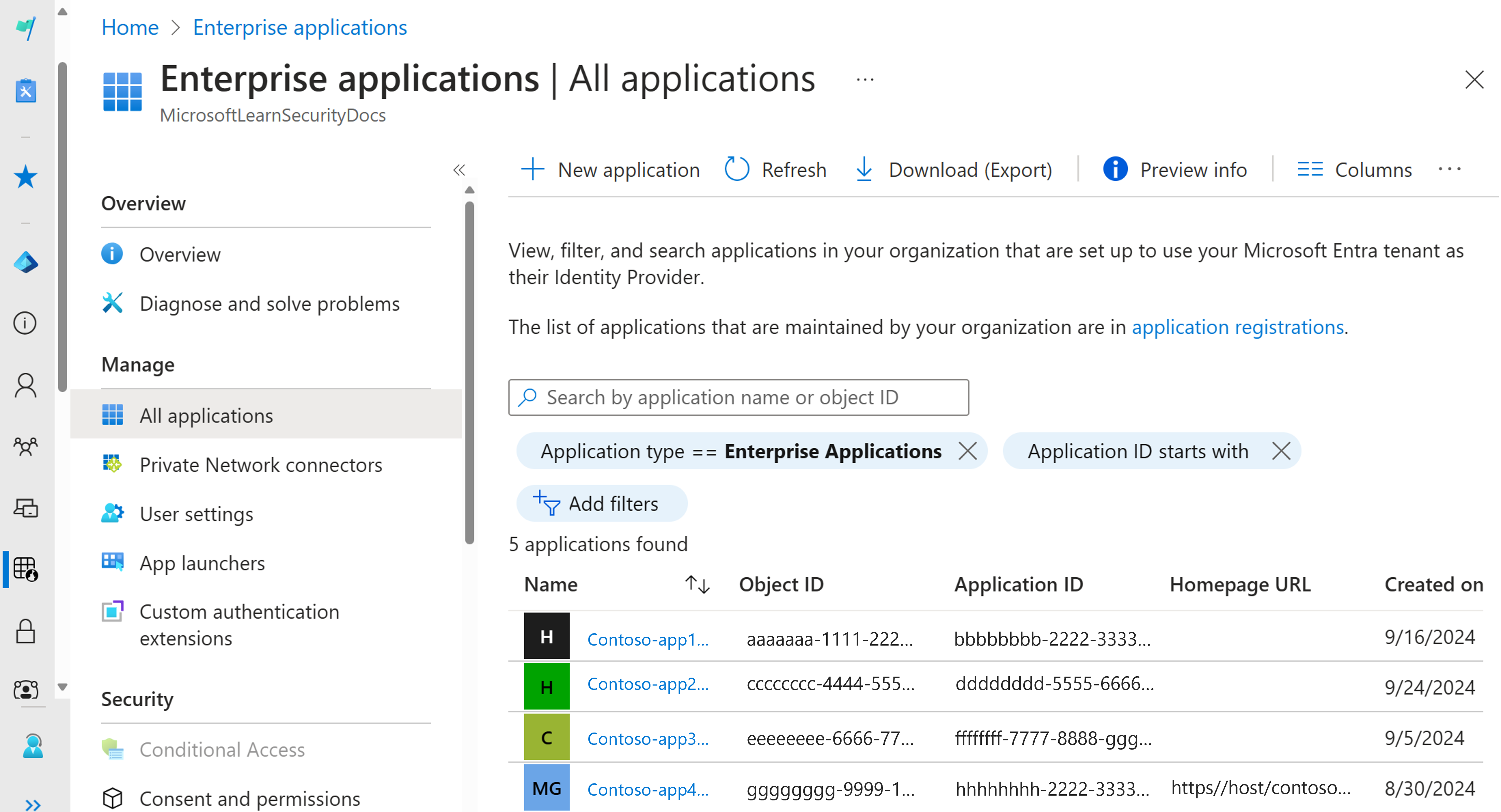
3. Microsoft Entra ID
Microsoft Entra ID, formerly Azure AD, provides identity and permissions management within the Microsoft ecosystem. It integrates tightly with Microsoft 365, making it a common choice for organizations already using Microsoft tools.
Permissions are managed through groups, roles, and conditional access policies. Administrators can control access to applications, data, and services based on identity and risk signals. This supports strong security postures, especially in enterprise environments.
While powerful, Entra ID permissions can become complex to manage without dedicated expertise. It focuses primarily on system and application access rather than employee-facing content governance.
Key features of Microsoft Entra ID
- Role and group-based access: Manage permissions across Microsoft services.
- Conditional access policies: Apply rules based on risk and context.
- Deep Microsoft integration: Works seamlessly with Microsoft 365 and Azure.
Best for: Organizations heavily invested in Microsoft infrastructure.
4. JumpCloud
JumpCloud positions itself as a directory platform that centralizes user identity and device management. Its permissions capabilities span systems, applications, and devices, offering broad control from a single console.
Administrators can manage access across Windows, macOS, Linux, and cloud tools. Permissions are often tied to device trust and user identity, which supports distributed teams and remote work scenarios.
JumpCloud provides flexibility but may require more setup and technical oversight. It focuses on IT control rather than content or collaboration governance, making it best suited for infrastructure-level access management.
Key features of JumpCloud
- Unified directory services: Manage users across systems and devices.
- Cross-platform support: Control access for diverse operating environments.
- Centralized administration: Apply permissions from one management layer.
Best for: IT teams managing mixed device and operating system environments.
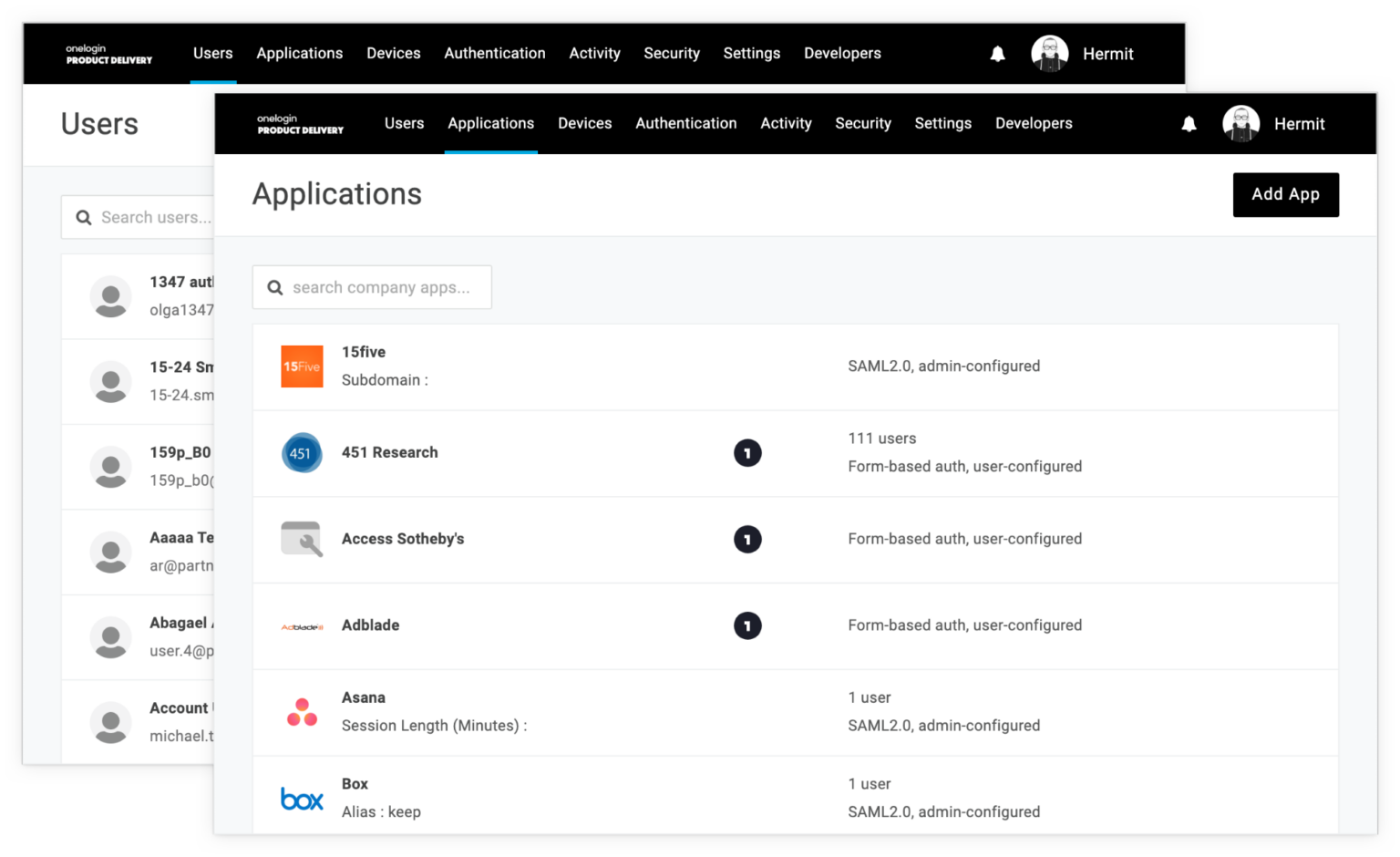
5. OneLogin
OneLogin is an identity and access management platform designed to simplify how organizations manage user access across applications. Its permissions management focuses on centralized control, automation, and policy enforcement.
With OneLogin, administrators can assign permissions through roles and groups, making it easier to grant consistent access as employees join, move roles, or leave the organization. Automated provisioning helps ensure users receive the right access on day one while reducing security gaps during offboarding.
OneLogin integrates with a wide range of cloud applications and identity providers. This makes it useful for organizations with diverse SaaS environments. Conditional access policies add another layer of control by factoring in user behavior and context.
While strong on application-level permissions, OneLogin does not extend deeply into content or collaboration governance. It works best when paired with an employee platform that manages internal knowledge and workflows.
Key features of OneLogin
- Role-based access assignment: Apply consistent permissions across applications.
- Automated user lifecycle management: Streamline onboarding and offboarding.
- Conditional access controls: Adjust permissions based on context.
Best for: Organizations that need streamlined access management for SaaS tools.
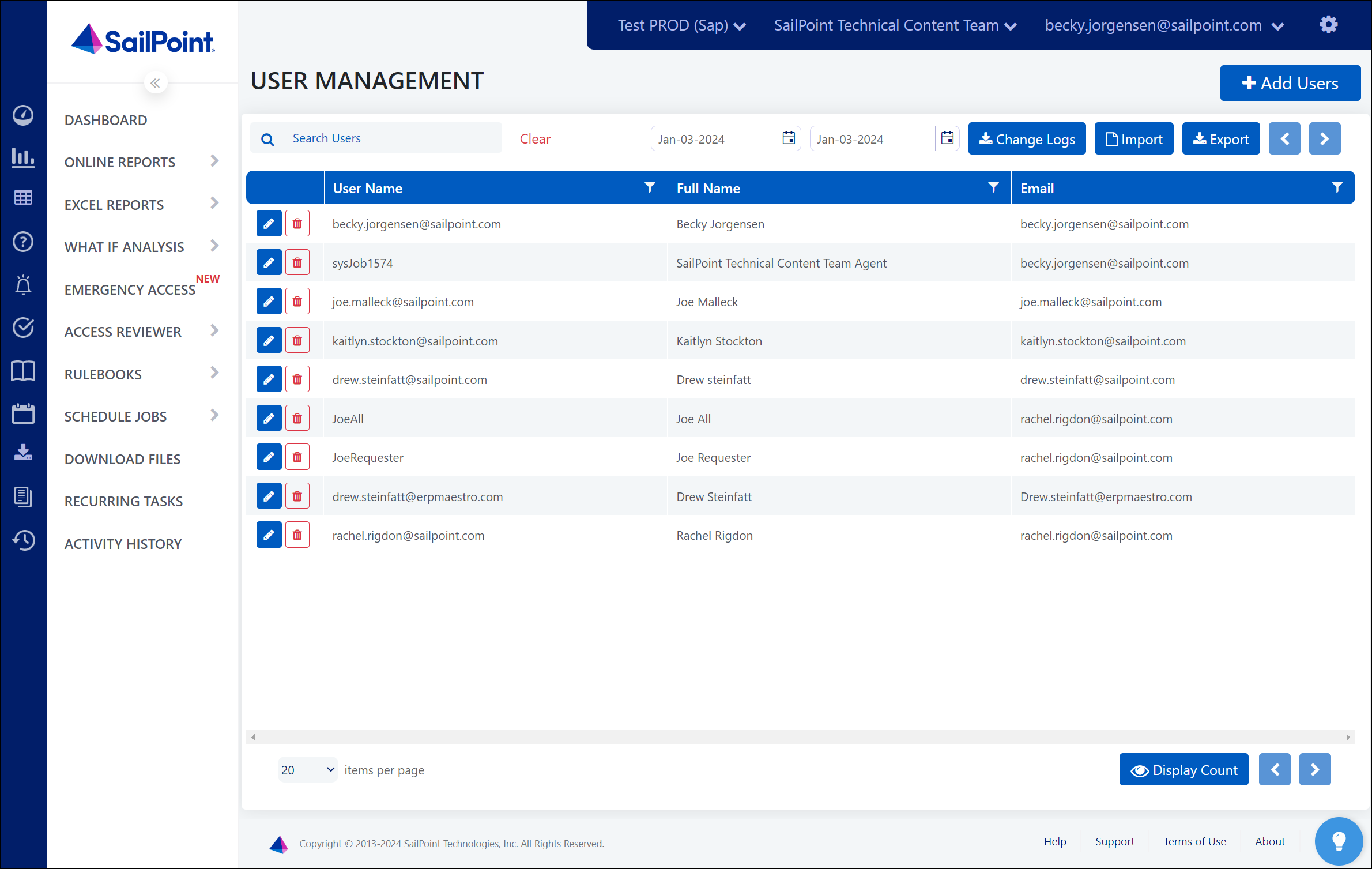
6. SailPoint
SailPoint focuses on identity governance and administration, with permissions management built around compliance, audits, and risk reduction. It is commonly used in large enterprises with complex regulatory requirements.
Permissions in SailPoint are managed through policies, roles, and certifications. Regular access reviews help organizations verify that users still need their assigned permissions. This reduces long-term risk and supports internal controls.
SailPoint excels at governance but can feel heavy for day-to-day employee access needs. Setup and administration often require dedicated resources. The platform prioritizes oversight and compliance over simplicity.
For organizations with strict governance requirements, SailPoint offers depth and structure. For employee-facing access management, it is typically part of a larger ecosystem.
Key features of SailPoint
- Access certifications: Run regular reviews to validate permissions.
- Policy-driven governance: Enforce consistent access rules.
- Compliance reporting: Support audits and regulatory needs.
Best for: Enterprises with complex compliance and governance requirements.
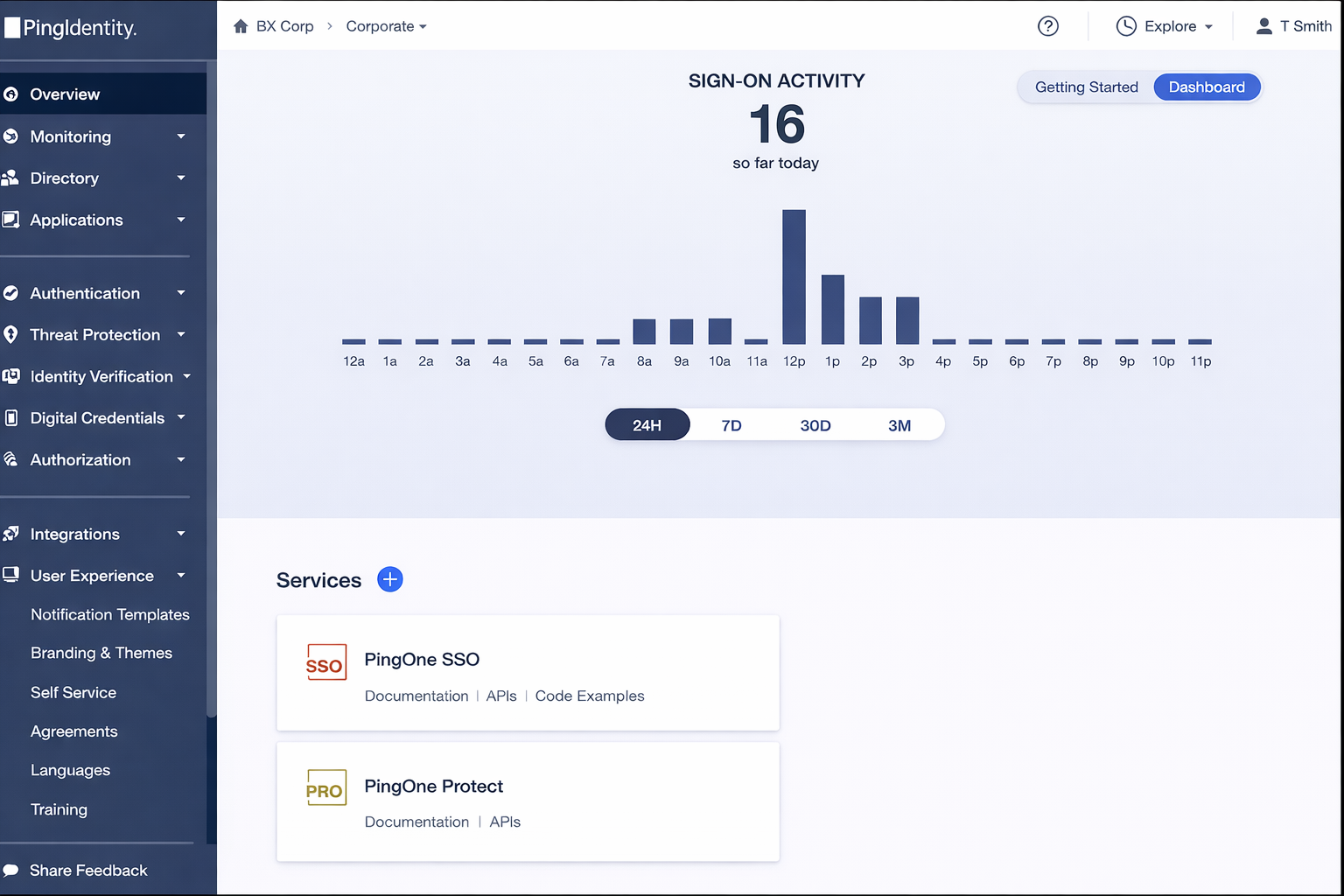
7. Ping Identity
Ping Identity provides identity security solutions with a strong emphasis on access control and authentication. Its permissions management supports secure access across applications and APIs.
Permissions are often managed through policies that consider user identity, device posture, and context. This allows organizations to apply fine-grained access rules without hardcoding permissions into each system.
Ping Identity integrates well with custom applications and hybrid environments. However, it is more security-focused than employee-focused. Managing internal content permissions typically requires complementary tools.
Ping Identity suits organizations that need flexible, policy-driven access controls across complex architectures.
Key features of Ping Identity
- Policy-based access management: Apply dynamic access rules.
- API and application support: Secure custom and third-party systems.
- Context-aware controls: Adjust access based on risk signals.
Best for: Organizations with custom applications and hybrid environments.
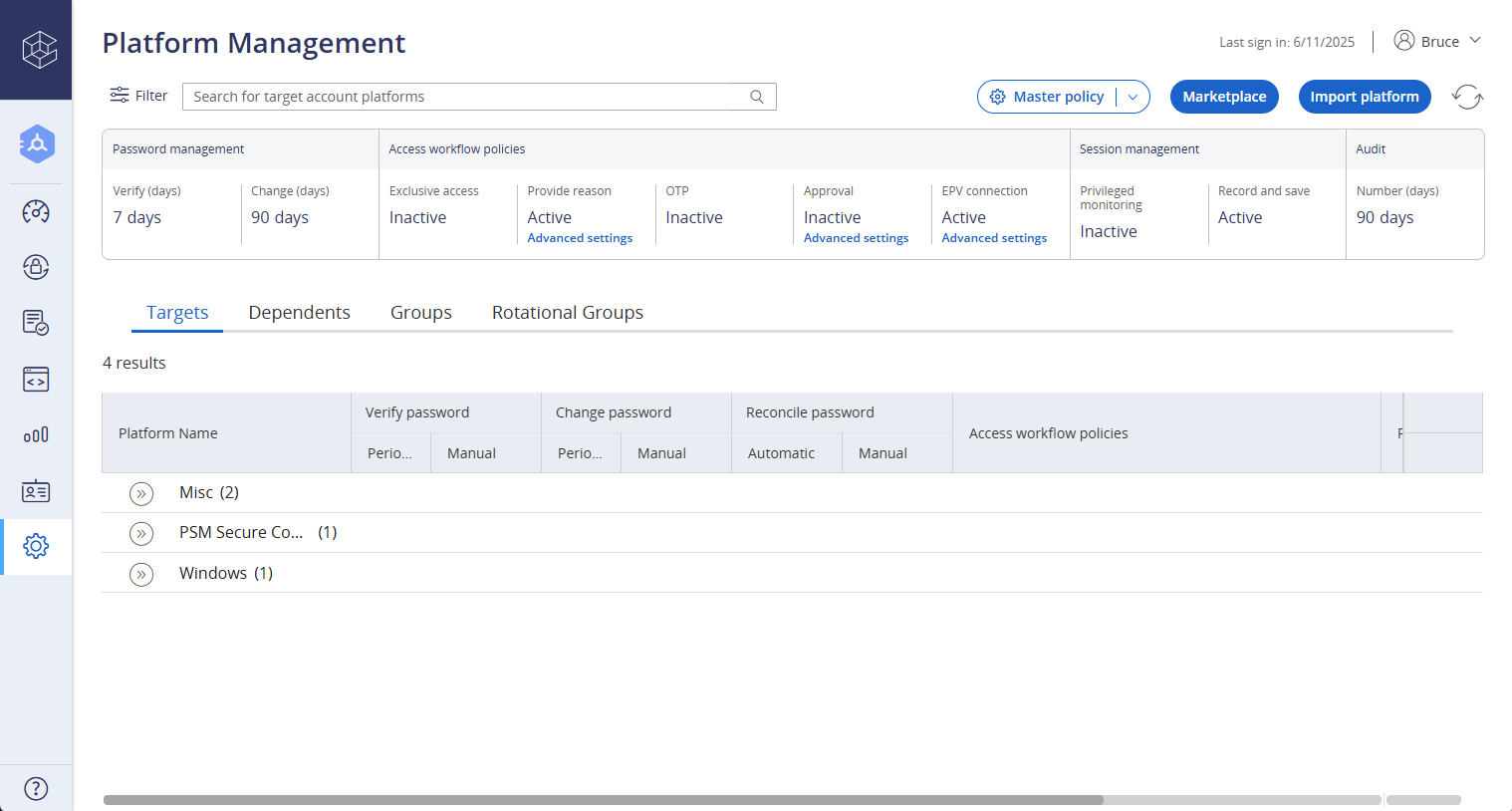
8. CyberArk
CyberArk specializes in privileged access management. Its permissions capabilities focus on securing high-risk accounts, systems, and credentials.
Rather than managing everyday employee access, CyberArk controls elevated permissions for administrators, service accounts, and sensitive systems. It limits standing privileges and enforces strict access workflows.
CyberArk is highly effective for reducing insider risk and protecting critical infrastructure. However, it is not designed to manage general content or collaboration permissions across an organization.
Most organizations use CyberArk alongside broader permissions or intranet platforms to cover everyday access needs.
Key features of CyberArk
- Privileged access controls: Secure high-risk accounts and systems.
- Session monitoring: Track and record privileged activity.
- Session monitoring: Reduce standing access rights.
Best for: Organizations securing administrative and privileged access.
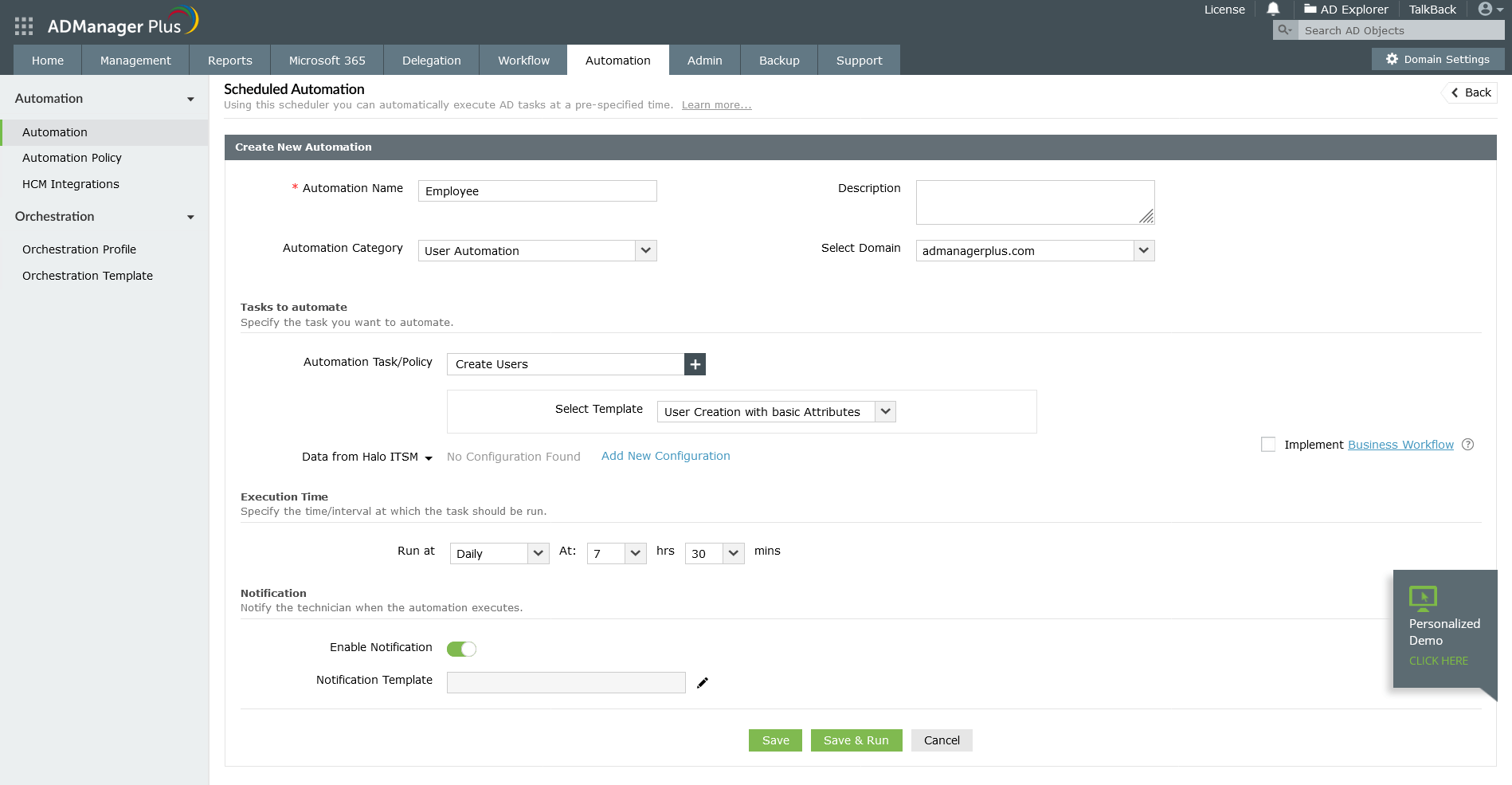
9. ManageEngine Identity Manager Plus
ManageEngine Identity Manager Plus offers a structured approach to user permissions management with a strong focus on identity lifecycle automation. It supports role-based access control across applications, directories, and systems, helping organizations reduce manual permission assignments.
Permissions are tied closely to HR-driven events. When an employee joins, changes roles, or leaves, access updates automatically based on predefined policies. This improves consistency and reduces delays that often frustrate employees during onboarding.
The platform includes reporting and access review features to support audits and internal controls. While powerful, the interface and configuration can feel complex for smaller teams. It works best when IT teams need deep control over identity workflows rather than employee-facing access experiences.
Key features of ManageEngine Identity Manager Plus
- HR-driven automation: Align permissions with employee lifecycle events.
- Role-based access control: Standardize access across systems.
- Compliance reporting: Support audits and reviews.
Best for: Organizations that need automated identity workflows tied to HR systems.
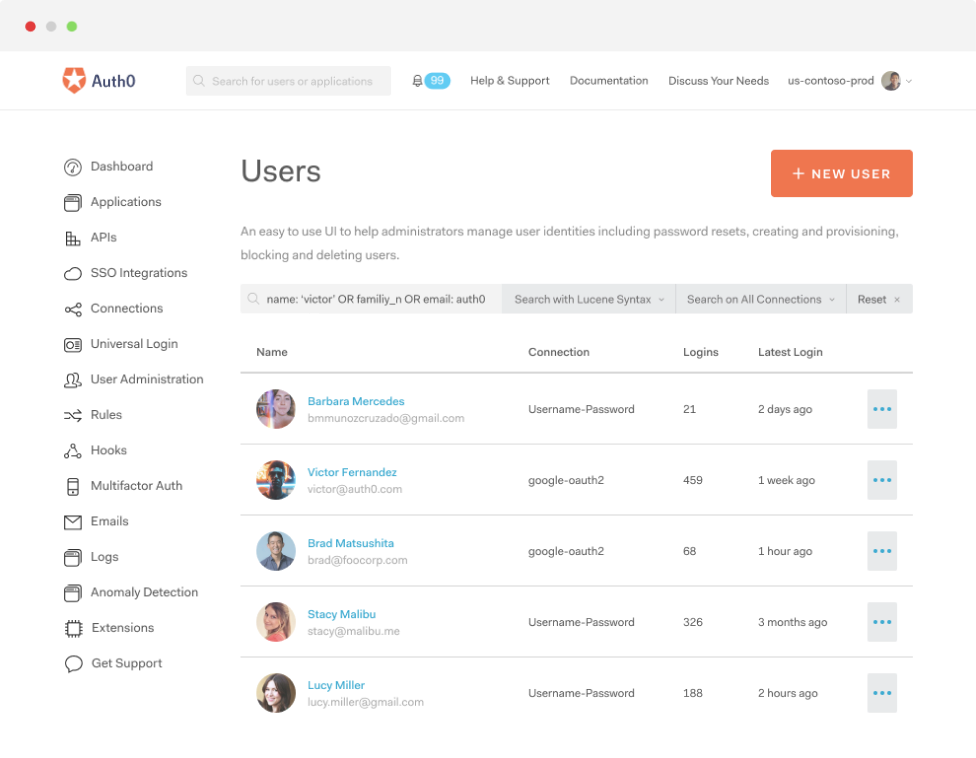
10. Auth0
Auth0 focuses on identity authentication and authorization, particularly for applications and digital products. Its permissions management is designed for developers who need fine-grained control over user access within custom applications.
Permissions are often implemented through scopes, roles, and policies defined at the application level. This allows precise control but requires technical setup and ongoing maintenance. Auth0 excels in developer flexibility rather than administrative simplicity.
For internal employee access, Auth0 typically supports specific applications rather than serving as a central permissions hub. It works well in organizations building custom tools but less so as a standalone employee access solution.
Key features of Auth0
- Role and scope-based permissions: Define access within applications.
- Developer-friendly APIs: Customize access logic.
- Scalable authentication: Support growing user bases.
Best for:Development teams managing access in custom-built applications.
11. IBM Security Verify
IBM Security Verify provides identity and access management with enterprise-grade security controls. Its permissions management supports access to applications, systems, and data through centralized identity policies.
The platform emphasizes risk-based access and governance. Administrators can define rules that adjust permissions based on user behavior, device trust, or location. This supports strong security postures in regulated environments.
IBM Security Verify is robust but can feel heavyweight. It often requires integration with other IBM tools and dedicated administration. Employee-facing permissions and content governance typically rely on additional platforms.
Key features of IBM Security Verify
- Risk-based access controls: Adjust permissions dynamically.
- Centralized identity policies: Manage access across systems.
- Enterprise security focus: Support regulated industries.
Best for: Large enterprises with complex security requirements.
Bringing it all together
User permissions management software plays a direct role in security, productivity, and employee confidence. When access aligns with responsibilities, teams move faster, and risks drop without adding friction.
Many tools in this space focus heavily on identity and application access. While effective, they often stop short of managing how employees interact with content, workflows, and shared knowledge.
This is where Axero takes a different approach. By embedding permissions into a central employee platform, Axero gives you control without complexity. Access supports collaboration, onboarding, and engagement, not just security checklists.
If you want permissions management that fits naturally into how your organization works, it starts with the right digital workplace foundation.
Book a demo today and see how Axero can help you manage access with clarity and confidence.






















 info@axerosolutions.com
info@axerosolutions.com 1-855-AXERO-55
1-855-AXERO-55



